- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
- RUCKUS Forums
- RUCKUS Technologies
- RUCKUS Self-Help
- Cloudpath | Error "Unable to authorize via SAML", ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
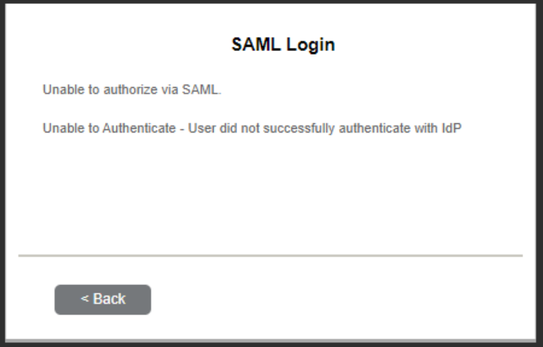
Cloudpath | Error "Unable to authorize via SAML", G-Suite Authentication fails
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2023 12:46 PM - edited 10-16-2023 12:49 PM
Issue: Users experiencing authentication failures when using SAML-based authentication, particularly with external services like G-Suite.
Root Cause: The Security Assertion Markup Language (SAML) relies on precise time synchronization between the systems involved (identity provider, service provider, and user's device) to ensure the security of authentication transactions.
Resolution:
Ensure Accurate Time Configuration:
- Confirm that both the Cloudpath instance and the virtual server have accurate time configurations.
- Point NTP configurations to a reliable NTP server, such as RUCKUS's public NTP server (ntp.ruckuswireless.com).
Automatic Time Synchronization:
- Set up automatic NTP synchronization to ensure consistent and accurate time across systems.
- Regularly monitor NTP synchronization to detect and address any time drift issues promptly.
Follow this guide for instructions on how to configure SAML services in RUCKUS Cloudpath.
How SAML Works:
Request Initiation:
- User requests access to a service.
- Service Provider (SP) redirects the user to the Identity Provider (IdP) for authentication.
Authentication:
- IdP authenticates the user by requesting credentials (e.g., username and password).
- IdP generates a SAML assertion containing authentication information encrypted with the SP's public key and user details.
SAML Assertion:
- SAML assertion includes a timestamp to ensure its freshness.
- If the SAML assertion is too old (beyond a defined time window), the assertion is considered invalid.
Response to Service Provider:
- IdP sends the SAML assertion back to the user's browser.
Access Granted:
- User's browser submits the SAML assertion to the SP.
- SP validates the assertion's authenticity and, if valid, grants access.
--
Orlando Elias
Technical Support
- Labels:
-
Cloudpath
-
RUCKUS Self-Help
-
AAA
2 -
Access points
48 -
Analytics
3 -
AP Certificate error
1 -
AP Controller Connectivity
5 -
AP Management
8 -
AP migration
1 -
AP reporting
1 -
API
2 -
Authentication Server
2 -
Client Management
1 -
Cloud
20 -
Cloud ICX
1 -
Cloudpath
23 -
Cluster synchronization
1 -
Deployment
2 -
Firmware Recommendation
1 -
Firmware Upgrade
5 -
Guest Access
2 -
ICX
73 -
ICX Switch Management
7 -
Installation
5 -
IoT
1 -
Licensing
1 -
Mobile Apps
2 -
Monitoring
1 -
Poe
2 -
RADIUS
2 -
Ruckus Cloud
1 -
RUCKUS Self-Help
209 -
Security
6 -
SmartZone or vSZ
64 -
Stacking
1 -
SZ ICX Connectivity
1 -
Traffic Management-
1 -
UMM
3 -
Unleashed
15 -
User Management
1 -
Venue Management
1 -
Wired Throughput
2 -
Wireless Throughput
1 -
WLAN Management
5 -
ZoneDirector
15
- « Previous
- Next »