- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
- RUCKUS Forums
- RUCKUS Technologies
- SZ / vSZ
- Re: vSZ & vSZ-D Tunnel mode not broadcasting SSID
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
vSZ & vSZ-D Tunnel mode not broadcasting SSID
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2021 07:47 PM
Hello,
I have both vSZ & Data Plane instances installed. I have an issue where when enabled in tunnel mode, it stops broadcasting the SSID for some strange reason. However when I do disable the tunneling method in vSZ - the AP starts to broadcast the SSID again. I have these instances installed on a bare metal @ a colocation center.
Any ideas about what it could be? I read a post on here about doing the:
get tunnelmgr
However I'm not entirely sure what it is that I'm looking for in this output. It says on that post that the AP may not be able to see the controller when doing data plane functionality?
I'm currently running this environment in Essentials mode.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2021 07:04 AM
The first step to see what the issue is would be to make ping and trace-router from AP to external vDP address (NAT IP), and from vDP to AP (external) IP address. From your description is not clear how AP is connected to the network.
Typical multisite configuration is that both sides (vSZ + vDP) and AP are behind Firewall with NAT. Management tunnel from AP to vSZ uses different ports and different destination IP (vSZ NAT IP). It works as much as I understand.
Data tunnel need to be established from AP internal IP through firewall with NAT to external vDP address (vDP NAT IP) and it uses different port. So you need to check all route -- if local firewall permits outgoing connection on ports UDP 23233/23233, if on vSZ/vDP side firewall allows this connection in and NATs it to vDP internal IP, that default route is set properly on vDP data interface, so it can send a reply to AP and firewall allows it... You have to look on both firewalls if tunnel setup actually is initiated and if replies are sent and received.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-24-2021 02:17 PM
Sorry about that, the AP is connected to a mikrotik router (basic config). With DHCP assigned for that AP.
I'll give the Mikrotik a look further on the AP's side. So when setting up the vDP's data interface, that needs to be set for an external NAT IP ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2021 01:54 PM
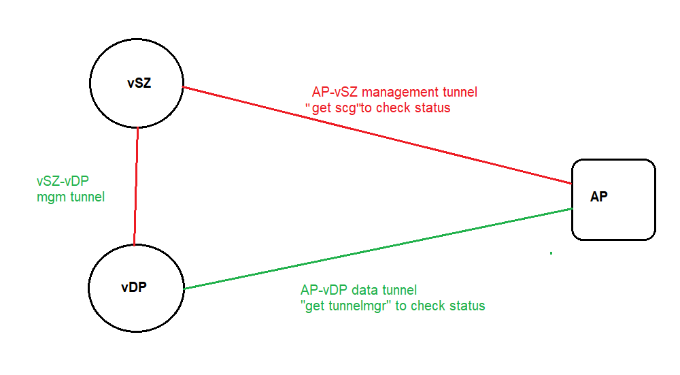
There will be 3 tunnel formed.
- Controller/management tunnel between v/SZ to v/SZ-D
- Controller tunnel between v/SZ - AP
- Data tunnel between AP - vSZ-D
Make sure these devices can reach each other for each tunnel.
Syamantak Omer
Sr.Staff TSE | CWNA | CCNA | RCWA | RASZA | RICXI
RUCKUS Networks, CommScope!
Follow me on LinkedIn
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-24-2021 02:00 PM
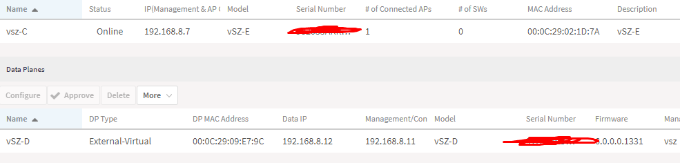
I'm able to ping the vSZ from the vDP. As well as from vDP to vSZ.
Doing the "Get scg" command via the AP:
------ SCG Information ------
SCG Service is enabled.
AP is managed by SCG.
State: RUN_STATE
Server List: 192.168.8.7,PUBLIC-IP
SSH tunnel connected to PUBLIC-IP
Failover List: Not found
Failover Max Retry: 2
DHCP Opt43 Code: 6
Server List from DHCP (Opt43/Opt52): Not found
SCG default URL: RuckusController
SCG config|heartbeat intervals: 30|30
SCG gwloss|serverloss timeouts: 1800|7200
Controller Cert Validation : disable
From the AP itself, these are located remotely. It shows the LAN IP 192.168.8.7 (vSZ) in the server list, but that's the LAN IP from the controller itself behind a router located at our colo.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-24-2021 02:03 PM
My server is a different IP than the NAT IP I assigned my vSZ. So do I need to remove the PUBLIC-IP of the controller above, and make that the server IP (which is my router) ?
Colo Topology:
Router <--- 123.45.6.7 - 123.45.6.11 (5 IP Block)
vSZ <---- LAN 192.168.8.7 -- (WAN)123.45.6.10
vDP <---- LAN 192.168.8.11
Port Forwards:
- vSZ >> 22,443
- vDP >> 23233
Remote Location:
My H510 (at a location) is pointed at the controller: 123.45.6.10
The LAN side behind my router
-
9210
1 -
AD
1 -
AP Controller Connectivity
2 -
AP Management
5 -
AP reporting
1 -
API Help
1 -
Client Management
4 -
er
1 -
Google
1 -
Guest Access
3 -
ICX Switch Management
1 -
IP Multicast
1 -
Proposed Solution
3 -
RADIUS
2 -
RUCKUS Self-Help
8 -
SmartZone
4 -
SmartZone or vSZ
6 -
Social Media
1 -
Solution Proposed
3 -
string
1 -
SZ ICX Connectivity
1 -
Traffic Management-
1 -
User Management
2 -
vSZ
2 -
Wifi
1 -
WLAN Management
2
- « Previous
- Next »

