This website uses cookies. By clicking Accept, you consent to the use of cookies. Click Here to learn more about how we use cookies.
- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- RUCKUS Forums
- RUCKUS Technologies
- SZ / vSZ
- vSZ-D Tunnelling WLAN with VLAN Tag What i am miss...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
vSZ-D Tunnelling WLAN with VLAN Tag What i am missing
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-23-2018 02:12 AM
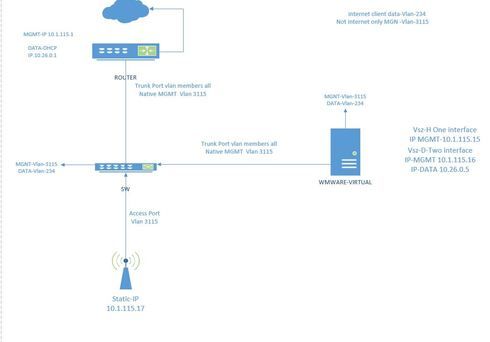
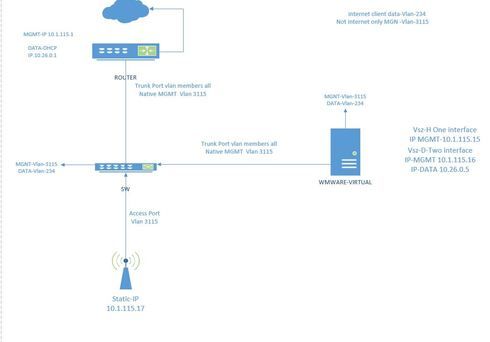
The problem is when i create WLAN and tagged it with DATA VLAN ID 234 , (i used Tunnel WLAN traffic to the controller) my client can't get IP address from DATA VLAN, try it with static IP address assignment, my device still can't ping my DATA VLAN Gateway 10.26.0.1
I look around the configuration and still not working. What i am missing
Vsz-H version 3.5.1.0.862
Vsz-D version 3.5.1.0.862
AP-R700 Router Cisco DHCP-SERVER and Gateway
SW-Juniper
Virtual :
Vsz-D Data interface IP 10.26.0.5
MGMT interface IP 10.1.115.16 Vsz-H
MGMT interface IP 10.1.115.15
AP IP 10.1.115.17
all port Trunk.
My Topology
I look around the configuration and still not working. What i am missing
Vsz-H version 3.5.1.0.862
Vsz-D version 3.5.1.0.862
AP-R700 Router Cisco DHCP-SERVER and Gateway
SW-Juniper
Virtual :
Vsz-D Data interface IP 10.26.0.5
MGMT interface IP 10.1.115.16 Vsz-H
MGMT interface IP 10.1.115.15
AP IP 10.1.115.17
all port Trunk.
My Topology
11 REPLIES 11
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2018 10:08 AM
Hi Lasha,
I can see/understand your diagram, but it appears you are missing some things.
In VMware, you need to setup a new port group for the DataPlane. You need to make this port
a trunk by allowing all VLANs. Enable Promiscuous mode and then, since you are running a
vSwitch, you need to go to the vSZ-D Console, and configure the data interface to tag the data
VLAN for it.
The Client WLAN VLAN should be different than the data VLAN from the data interface. You don't
want your client having access to that VLAN I'd assume.
To recap:
1 - Create new portgroup with All VLANs allowed and promiscuous mode accept in the security tab.
2 - Console to the vSZ-D and go to configure, interface data, VLAN 234 to tagthe data interface VLAN.
3 - Create a new VLAN for the clients and then configure that on the AP so thatthey get their IPs from there. The vSZ-D data interface VLAN and theclient access VLAN should never be the same (not that they can't).
4 - Ensure the switch port allows the newly created client VLAN.
5 - Ensure DHCP is set for the new VLAN, not VLAN 234 as that is the interfaceof the vSZ-D Data Interface.
6 - Ensure the AP can talk to the vSZ-D Data interface and the controlinterface.
For reference, from the AP to the vSZ-D Data Interface, by default, you should allow ports 23233 on both TCP and UDP.
From the AP to the control plane, you need port 22, 443, and any other port you may require for captive portals, see the firewall configuration guide on our support site under Best Practice Documents section.
https://support.ruckuswireless.com/products/116-bpg_smartzone
I hope this helps.
I can see/understand your diagram, but it appears you are missing some things.
In VMware, you need to setup a new port group for the DataPlane. You need to make this port
a trunk by allowing all VLANs. Enable Promiscuous mode and then, since you are running a
vSwitch, you need to go to the vSZ-D Console, and configure the data interface to tag the data
VLAN for it.
The Client WLAN VLAN should be different than the data VLAN from the data interface. You don't
want your client having access to that VLAN I'd assume.
To recap:
1 - Create new portgroup with All VLANs allowed and promiscuous mode accept in the security tab.
2 - Console to the vSZ-D and go to configure, interface data, VLAN 234 to tagthe data interface VLAN.
3 - Create a new VLAN for the clients and then configure that on the AP so thatthey get their IPs from there. The vSZ-D data interface VLAN and theclient access VLAN should never be the same (not that they can't).
4 - Ensure the switch port allows the newly created client VLAN.
5 - Ensure DHCP is set for the new VLAN, not VLAN 234 as that is the interfaceof the vSZ-D Data Interface.
6 - Ensure the AP can talk to the vSZ-D Data interface and the controlinterface.
For reference, from the AP to the vSZ-D Data Interface, by default, you should allow ports 23233 on both TCP and UDP.
From the AP to the control plane, you need port 22, 443, and any other port you may require for captive portals, see the firewall configuration guide on our support site under Best Practice Documents section.
https://support.ruckuswireless.com/products/116-bpg_smartzone
I hope this helps.
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-07-2018 12:52 PM
Micheal, can you explain better how to make the data interface be a trunk port ?
I was only able to ''tag'' one vlan on it, wit the command vlan "X".
I was only able to ''tag'' one vlan on it, wit the command vlan "X".
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2019 01:38 PM
This post helped me figure out the vSZ-D configuration. My ap's have establed GRE tunnels back to the dataplane. Thanks!
I will say that the ap's did not establish the GRE tunnel until after a wlan configured for tunneling was put in place.
I will say that the ap's did not establish the GRE tunnel until after a wlan configured for tunneling was put in place.
Anonymous
Not applicable
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-07-2018 12:45 PM
Thank you Michael, this should be in the documention, very helpful !!!
Can you clarify, because I not able to make my vSZ-DP, data interface be a trunk port... I can only "tag'' one vlan with the command vlan "X", and that is it, I tried different syntax but did not work....
So, how can I have differents ssid with differents vlan pools, and make it enter the data interface from my DP ??
I understand that I should have my vnic as a trunk port, but I do not understand how to make the data interface be a trunk port.
Here my config of it:
data iface:
name: pow0
vlan: 0
proto: static
addr: 192.168.1.117
netmask: 255.255.255.0
gateway: 192.168.1.1
Can you clarify, because I not able to make my vSZ-DP, data interface be a trunk port... I can only "tag'' one vlan with the command vlan "X", and that is it, I tried different syntax but did not work....
So, how can I have differents ssid with differents vlan pools, and make it enter the data interface from my DP ??
I understand that I should have my vnic as a trunk port, but I do not understand how to make the data interface be a trunk port.
Here my config of it:
data iface:
name: pow0
vlan: 0
proto: static
addr: 192.168.1.117
netmask: 255.255.255.0
gateway: 192.168.1.1
Labels
-
9210
1 -
AD
1 -
AP Controller Connectivity
2 -
AP Management
5 -
AP reporting
1 -
API Help
1 -
Client Management
4 -
er
1 -
Google
1 -
Guest Access
3 -
ICX Switch Management
1 -
IP Multicast
1 -
Proposed Solution
3 -
RADIUS
2 -
RUCKUS Self-Help
8 -
SmartZone
4 -
SmartZone or vSZ
6 -
Social Media
1 -
Solution Proposed
3 -
string
1 -
SZ ICX Connectivity
1 -
Traffic Management-
1 -
User Management
2 -
vSZ
2 -
Wifi
1 -
WLAN Management
2
- « Previous
- Next »

