- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
- RUCKUS Forums
- RUCKUS Technologies
- SZ / vSZ
- Rogue APs detection / exceptions
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Rogue APs detection / exceptions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-19-2023 04:34 AM
Hi to all... on the same area i have two differnet networks one with vSZ and some ruckus APs and another network with Unifi Controller and APs... i can see that ruckus detect many of the unifis as Rogue and probably blocks them.. (i cannot fully understand what 'block' means)... i found the WIPS rules but can i add some exceptions so any of the unifi's are not detected as rogues?
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-19-2023 07:01 AM
Hello @gsfakian
- SZ will send malicious list (that include Ruckus and 3rd party AP) to Ruckus AP terminating on the controller in every 15 minutes.
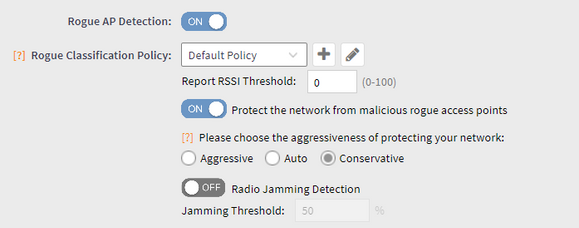
- The malicious list pushed from SZ consists of BSSIDs only and AP will send broadcast deauthentication frame, when "Protect the network" function is enabled, during the background scan.
Please refer the below Knowledge base article to configure the Rogue Detection policy.
https://support.ruckuswireless.com/articles/000010538
You can configure the rogue classification policy as "Known" for the Unify APs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-20-2023 12:14 AM
Hi @gsfakian
When the WIPS is enabled, Ruckus APs will try to scan and detect the Rogue APs, which are basically 3rd party APs which is broadcasting nearby.
Based on the settings configured, Ruckus APs are capable of "Just to detect and notify" or "Detect and block it".
Ruckus APs will send a deauth packets using the 3rd party APs BSSID, so that your network clients or any clients able to receive this packet from Ruckus AP will not be able to connect to the SSID which is broadcasting from the Unifi AP.
On the Zone settings, if you have "Rogue AP Detection" and "Protect the network from malicious rogue access points" enabled, then the AP will send deauth blocking the clients to connect to Unifi AP.
In that case, go to Rogue Device list >> Select the Unifi APs >> Select "Mark as known".
Or you can simple disable the option "Protect the network from malicious rogue access points" on the zone settings.
-
9210
1 -
AD
1 -
AP Controller Connectivity
2 -
AP Management
5 -
AP reporting
1 -
API Help
1 -
Client Management
4 -
er
1 -
Google
1 -
Guest Access
3 -
ICX Switch Management
1 -
IP Multicast
1 -
Proposed Solution
3 -
RADIUS
2 -
RUCKUS Self-Help
8 -
SmartZone
4 -
SmartZone or vSZ
6 -
Social Media
1 -
Solution Proposed
3 -
string
1 -
SZ ICX Connectivity
1 -
Traffic Management-
1 -
User Management
2 -
vSZ
2 -
Wifi
1 -
WLAN Management
2
- « Previous
- Next »