This website uses cookies. By clicking Accept, you consent to the use of cookies. Click Here to learn more about how we use cookies.
- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- RUCKUS Forums
- RUCKUS Technologies
- ZD
- Re: Client deauth when Force DHCP enabled [issue E...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Client deauth when Force DHCP enabled [issue ER-4992 is back]
Anonymous
Not applicable
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-16-2018 02:10 AM
Android client is deauthenticated when roaming within same subnet. This behaviour is reproducible when Force DHCP enabled.
Issue ER-4992 was fixed in firmware 9.13.3 (MR3 Refresh4) but is back in latest firmware 10.1.1.0 for ZD1200.
When Force DHCP is disabled, no issues with roaming. But this will cause unwanted clients with static IPs connecting to our network.
Background of ER-4992:
Resolved an issue where, if Force DHCP was enabled, clients would be deauthenticated after roaming to another AP if the VLAN after roaming was the same as the previous VLAN. [ER-4992]
Issue ER-4992 was fixed in firmware 9.13.3 (MR3 Refresh4) but is back in latest firmware 10.1.1.0 for ZD1200.
When Force DHCP is disabled, no issues with roaming. But this will cause unwanted clients with static IPs connecting to our network.
Background of ER-4992:
Resolved an issue where, if Force DHCP was enabled, clients would be deauthenticated after roaming to another AP if the VLAN after roaming was the same as the previous VLAN. [ER-4992]
5 REPLIES 5
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2018 09:51 AM
That's definitely a bug! Do you have a case, and I would insist on an image with the bug fix?
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-08-2018 01:43 AM
Hi Michael, See my reply below.
Anonymous
Not applicable
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-08-2018 01:43 AM
Here's the case number: Case #00822526
Steps to reproduce:
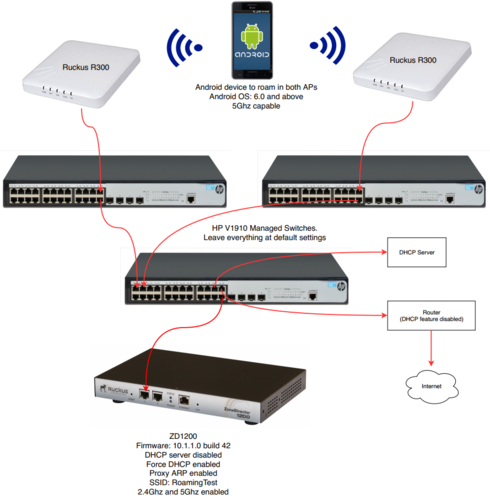
- Setup the topology as attached in picture below. Everything in the SAME subnet.
- Setup ZD1200 with firmware 10.1.1.0 build 42. Configure your WLAN SSID using the config below.
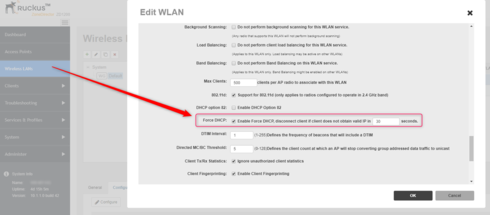
- Go to Wireless LANs > Edit WLAN > enable “Enable Force DHCP, disconnect client if client does not obtain valid IP in 30 secs”. See screenshot below.
- Your wifi should be internet enabled (means user can browse any internet websites from their device)
- Connect an Android device to your wifi. Open Terminal on Android and ping your router IP continously.
- Make the Android device roam from one AP to another. If you have space constraints, contact Ruckus Development/Engineering team lead on best practices to test device roaming.
- Notice after roaming to another AP, the Android device cannot ping router IP. Android device has NO internet. [Not OK].
- Go to Wireless LANs > Edit WLAN > DISABLE “Enable Force DHCP, disconnect client if client does not obtain valid IP in 30 secs”.
- Android device immediately resumes pinging router IP.
- Go to Wireless LANs > Edit WLAN > ENABLE “Enable Force DHCP, disconnect client if client does not obtain valid IP in 30 secs”.
- Immediately, Android device cannot ping router IP. Android device has NO internet. [Not OK].
- Question: Why does “Enable Force DHCP” affects android devices?
WLAN Service:
ID:
1:
NAME = Employees
Tx. Rate of Management Frame(2.4GHz) = 24.0Mbps
Tx. Rate of Management Frame(5GHz) = 24.0Mbps
Beacon Interval = 100ms
SSID = Employees
Description = Employees
Type = Standard Usage
Authentication = open
Encryption = wpa2
Algorithm = aes
Passphrase = hidden
FT Roaming = Disabled
802.11k Neighbor report = Disabled
Web Authentication = Disabled
Authentication Server = Disabled
Called-Station-Id type = wlan-bssid
Tunnel Mode = Disabled
Background Scanning = Enabled
Max. Clients = 500
Isolation per AP = Disabled
Isolation across AP = Disabled
Zero-IT Activation = Disabled
Priority = High
Load Balancing = Enabled
Band Balancing = Enabled
Dynamic PSK = Disabled
Rate Limiting Uplink = Disabled
PerSSID Rate Limiting Uplink = 0
Rate Limiting Downlink = Disabled
PerSSID Rate Limiting Downlink = 0
Auto-Proxy configuration:
Status = Disabled
Inactivity Timeout:
Status = Enabled
Timeout = 30 Minutes
VLAN-ID = 1
Dynamic VLAN = Disabled
Closed System = Disabled
Https Redirection = Disabled
OFDM-Only State = Enabled
Multicast Filter State = Disabled
802.11d State = Enabled
Force DHCP State = Enabled
Force DHCP Timeout = 30
DHCP Option82:
Status = Disabled
Option82 sub-Option1 = Disabled
Option82 sub-Option2 = Disabled
Option82 sub-Option150 = Disabled
Option82 sub-Option151 = Disabled
Ignore unauthorized client statistic = Enabled
STA Info Extraction State = Enabled
BSS Minrate = 24.0 Mbps
DTIM period = 1
Directed MC/BC Threshold = 5
Call Admission Control State = Disabled
PMK Cache Timeout= 720 minutes
PMK Cache for Reconnect= Enabled
NAS-ID Type= wlan-bssid
Roaming Acct-Interim-Update= Disabled
PAP Message Authenticator = Enabled
Send EAP-Failure = Disabled
L2/MAC = Blacklist
L3/L4/IP Address = No ACLS
L3/L4/IPv6 Address = No ACLS
Precedence = Default
Proxy ARP = Enabled
Device Policy = No ACLS
Vlan Pool = No Pools
Role based Access Control Policy = Disabled
SmartRoam = Enabled Roam-factor = 4
White List = No ACLS
Application Recognition & Control = Enabled
Apply ARC Policy = NO POLICY
Client Flow Data Logging = Disabled
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-08-2018 09:00 AM
Great, please open a ticket and provide your information, so one of our TSEs can assist with tracing the activity.
Labels
-
DHCP
1 -
IP lease
1 -
license snmp
1 -
Proposed Solution
1 -
Ruckus
1 -
server
1 -
VLAN
1 -
wap
1 -
zone director
1 -
ZoneDirector
1