This website uses cookies. By clicking Accept, you consent to the use of cookies. Click Here to learn more about how we use cookies.
- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- RUCKUS Forums
- RUCKUS Technologies
- Access Points
- Windows clients sending windows credentials
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Windows clients sending windows credentials
Anonymous
Not applicable
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-12-2018 03:08 PM
We're trying a number of options for a space that's almost all "guest" access, and since web portals are awful with HTTPS everywhere, we're trying 802.1x EAP auth to a radius server.
For OS-X, it's been working great. User picks network, types in their credentials from our partner that runs the radius server, and away they go. Windows folks though... some connect with no issues. Others seem to be sending what appear to be their actual windows domain credentials (there are "\\" in the username, etc.) as opposed to sending the email/password that the on-site folks provide them. I am not a windows person, what is this fluke and on the AP side of things, is there any way to prevent this behavior?
For OS-X, it's been working great. User picks network, types in their credentials from our partner that runs the radius server, and away they go. Windows folks though... some connect with no issues. Others seem to be sending what appear to be their actual windows domain credentials (there are "\\" in the username, etc.) as opposed to sending the email/password that the on-site folks provide them. I am not a windows person, what is this fluke and on the AP side of things, is there any way to prevent this behavior?
3 REPLIES 3
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-14-2018 12:06 AM
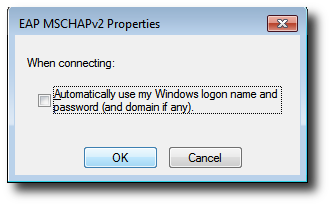
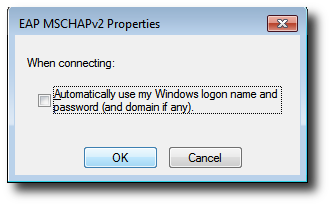
By default Windows will send domain credentials, if its managed by AD. You can check out this option from LAN connection properties.
Thanks
Karthik.
Thanks
Karthik.
Anonymous
Not applicable
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-28-2018 02:48 AM
This is not the major problem. I have the similar issue a few months ago. The option EAP deleted always may be due to antivirus. I have managed this problem with the help of Windows 10 support number . You may try this.
. You may try this.
 . You may try this.
. You may try this. Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-29-2018 10:40 PM
Do NOT click on the link in the above post. This person is posting this link on multiple Get Satisfaction forums, including the on I frequent (ViaSat), so I'm making sure to warn others to not click on that link. It's a phishing scam.
Labels
-
Access points
1 -
AP Controller Connectivity
2 -
AP Management
6 -
AP migration
1 -
Authentication Server
1 -
cli
1 -
Client Management
2 -
Firmware Upgrade
2 -
Guest Pass
1 -
I live in
1 -
Installation
3 -
IP Multicast
1 -
Poe
3 -
Proposed Solution
2 -
R320 SLOW SPEED
1 -
R550
1 -
R610
1 -
R650
2 -
R750
2 -
Ruckus
1 -
Security
1 -
SmartZone
1 -
Solution Proposed
2 -
SSH
1 -
Unleashed
1 -
User Management
1 -
Wireless Throughput
1 -
WLAN Management
2 -
ZoneDirector
1
- « Previous
- Next »

