- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
- RUCKUS Forums
- RUCKUS Technologies
- Access Points
- Re: Connection between AP and vSZ
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Connection between AP and vSZ
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-15-2016 08:30 AM
We tried
· DHCP option 43 as described in https://support.ruckuswireless.com/answers/000003197
· manually add the director ip (set director ip x.x.x.x) on the ap
but the AP doesn’t connect and/or perform no firmware update.
When we first connect the AP internally to the vSZ and move the AP to the appropriate Zone, it will work at the customer ́s Network.
Did we miss something or doing it wrong?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-15-2016 09:30 AM
Enabling LWAPP2SCG
If the LWAPP2SCG application is pre-installed but disabled in your controller
release, do the following to enable it:
1 Log on to the controller’s console.
2 Enter en to enable privileged mode.
3 Enter config.
4 Enter lwapp2scg.
5 Enter policy accept-all.
You have completed enabling the LWAPP2SCG application on the controller.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-15-2016 10:03 AM
1. From some version (I think 3.2) you need additional ports to be opened on firewall for firmware download (16384-65000 Tcp). When AP is already initially connected to v-SZ (and has proper v-SZ image), it works without troubles, but firmware upgrade to the next version will fail.
2. If you have out of box APs which has been delivered for use with ZD, you need both Ruckus vendor options on DHCP, directing to same v-SZ IP. ZD APs are interested in one option, v-SZ - in second. So in the beginning AP with universal image gets v-SZ IP as a ZD IP, contacts v-SZ and gets converted.
Ports to be forwarded are:
443 TCP, 22 tcp, 91 tcp, 123 tcp, 1812-1813, tcp 23233 udp, 23232 Tcp, 80 tcp, 6868 tcp, 12223 Tcp, 161 Tcp, 21 Tcp, 8080 Tcp, 8443 Tcp, 8099-8111 Tcp, 9997-9998 Tcp, 9080 Tcp, 9443 Tcp, 1143 Tcp, udp, 8090 Tcp, 12223 Tcp, 16384-65000 Tcp.
Additional comment -- if AP was in fact connected to ZD, even after factory reset, when connected to vSCG, it will not work properly. You need to reset it to factory default again after it get's v-SZ firmware, only than it will work properly.
Hope it helps,
Eizens
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-16-2016 04:13 AM
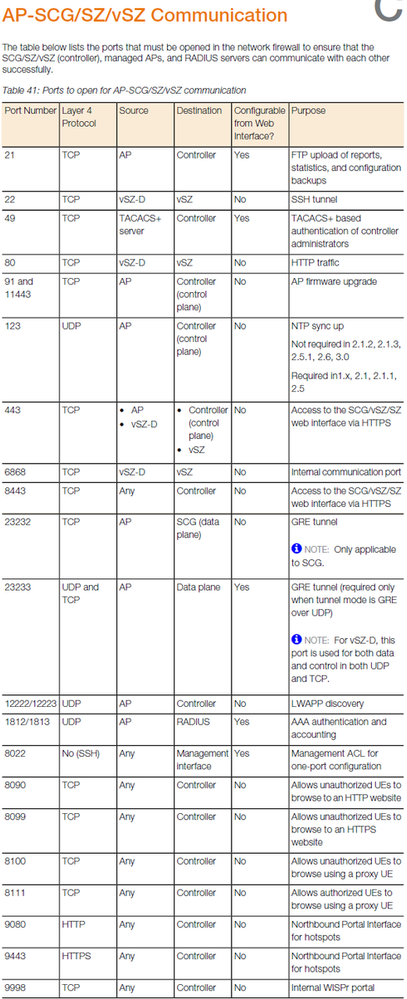
Note: Taken from SCG/vSZ-H 3.2 Administrator Guide
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-16-2016 08:12 AM
LWAPP2SCG is active for all APs.
We configured 03 as well as 06 in DHCP option 43
Here a picture of our configuration:
But it still does not work...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-16-2016 09:20 AM
Zone Config Example
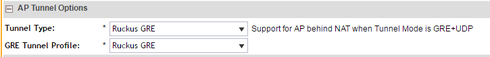
Ruckus GRE Profile Example
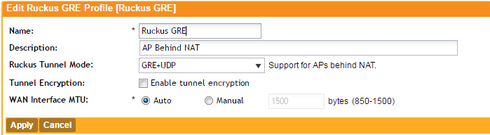
I have had this working but my data plane on the SCG had a public facing IP and the AP' pointed to that IP.
Note: the Ruckus GRE Profile needs to be configured prior to choosing it in the zone.
As a side measure I would recommend that you sniff to see what's happening with the lwapp frame from the AP i.e. is the AP sending one as I have seen it before when certain AP's dont and you haev to factory reset them in this case.
Also sniff the SCG data plane and see if the SCG is recieving the lwapp frame and what is happening with it when recieved if its being received at all.
Good luck
-
Access points
1 -
AP Controller Connectivity
2 -
AP Management
6 -
AP migration
1 -
Authentication Server
1 -
cli
1 -
Client Management
2 -
Firmware Upgrade
2 -
Guest Pass
1 -
I live in
1 -
Installation
3 -
IP Multicast
1 -
Poe
3 -
Proposed Solution
2 -
R320 SLOW SPEED
1 -
R550
1 -
R610
1 -
R650
2 -
R750
2 -
Ruckus
1 -
Security
1 -
SmartZone
1 -
Solution Proposed
2 -
SSH
1 -
Unleashed
1 -
User Management
1 -
Wireless Throughput
1 -
WLAN Management
2 -
ZoneDirector
1
- « Previous
- Next »


