- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
- RUCKUS Forums
- RUCKUS Technologies
- Access Points
- To configure a Zone Director 1200 should I attach ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
To configure a Zone Director 1200 should I attach it to a Trunk Port on my core
switch so that i can broadcast different VLANs on WIfi
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-21-2018 08:37 AM
More so are the access points supposed to be attached on a trunk port or access port to broadcast different SSIDs with different VLANs
I have R500 and T300 and R700 with version Version 200.3.9.13.228 can they be managed by a ZD with 10.1.1.0 build 42
and how do I get the build number of the access points and is version different from the Bundled Firmware
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-21-2018 09:13 AM
You only need to connect the Zone Director to a Trunk port carrying WLAN service VLAN's if you plan to tunnel traffic from the AP's to the ZD. In general tunnel is only useful to solve some specific Layer 3 issues or if you require all data be sent to the data center.
Normally WLAN's/SSID's are configure for local breakout so that traffic from clients connected to those WLAN's exit the AP directly into the local network. In this case if you plan to segregate client traffic into different VLANs then the AP's must be connected to Trunk ports that carry these VLAN's as tagged. When you configure a WLAN/SSID with a VLAN client traffic sent to the AP will be tagged on egress into the AP and will be forwarded out the WAN port (normally the Ethernet port except with mesh which is always a trunk connection) tagged as configured.
For simplified installation it is best to leave the AP management as untagged. This will put AP management traffic, including ZD control, into the switch port on the native VLAN. This can be tagged in the switch if needed by network design, but requiring AP's to tag management traffic makes installing AP's and dealing with factory defaulted AP's more complicated as by default AP management traffic is untagged.
Those AP models are supported on ZD version 10.1.1.0.
Which AP's are supported on a given version of ZD code can be determined by reading the Release notes for each ZD version. Release notes are available on the support site.
Code 200.3 is unleashed code. As far as I know you must first upgrade these AP's to standalone code (version 100.x) to connect to a ZD. Please check this article:
Converting Ruckus Unleashed AP to Standalone AP
https://support.ruckuswireless.com/articles/000005193
Once AP's Discover the ZD (by being in same IP subnet/vlan, using DHCP option43 or using manual command set director ip
Your current software version is 10.0.1.0 build 35. To see the access points that can be managed, click here
Current SoftwareI hope this answers your questions.
Thanks for choosing Ruckus Networks, an Arris company.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-04-2019 12:57 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-04-2019 11:44 AM
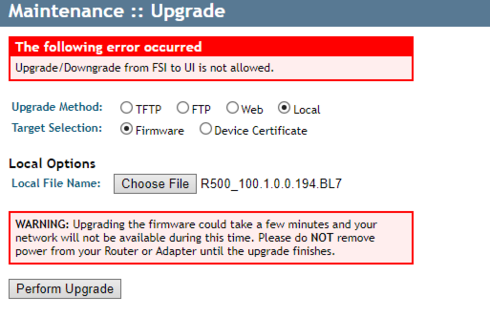
To improve security Ruckus introduced certificate sighed firmware image to prevent introducing a hacked version of code into the AP.
There are 3 types of firmware versions:
UI -Unsigned Image - original type without certificate signed
ISI - Intermediate signed certificate - a bridge between UI and FSI allowing upgrade or downgrade to either.
FSI - Fully Signed Certificate
The rules are you can only upgrade or downgrade from FSI to ISI or from UI to ISI
AP standalone code 100.x is UI code so you cannot download an FSI image.
Starting in version 104.x AP images are ISI.
So try using a newer version of AP code (104 or above)
To verify which type of AP firmware you have you can use the: fw show all command from the AP CLI
ZD AP code 9.13. and Unleashed 200.2 introduced as ISI, either of these version can be used as bridges to newer FSI version of firmware or to go back to older UI versions of code.
This data should be available in the Release notes for each version
https://support.ruckuswireless.com/documents/1134-access-point-104-0-0-0-1347-release-notes
Page 8
• AP Image Signing
Improves security by requiring verification of AP firmware images to ensure the
file has not been modified and that the source code executed by the system is
authentic code provided by Ruckus Wireless.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-27-2018 01:53 PM
-
Access points
1 -
AP Controller Connectivity
2 -
AP Management
6 -
AP migration
1 -
Authentication Server
1 -
cli
1 -
Client Management
2 -
Firmware Upgrade
2 -
Guest Pass
1 -
I live in
1 -
Installation
3 -
IP Multicast
1 -
Poe
3 -
Proposed Solution
2 -
R320 SLOW SPEED
1 -
R550
1 -
R610
1 -
R650
2 -
R750
2 -
Ruckus
1 -
Security
1 -
SmartZone
1 -
Solution Proposed
2 -
SSH
1 -
Unleashed
1 -
User Management
1 -
Wireless Throughput
1 -
WLAN Management
2 -
ZoneDirector
1
- « Previous
- Next »

