This website uses cookies. By clicking Accept, you consent to the use of cookies. Click Here to learn more about how we use cookies.
- Community
- RUCKUS Technologies
- RUCKUS Lennar Support
- Community Services
- RTF
- RTF Community
- Australia and New Zealand – English
- Brazil – Português
- China – 简体中文
- France – Français
- Germany – Deutsch
- Hong Kong – 繁體中文
- India – English
- Indonesia – bahasa Indonesia
- Italy – Italiano
- Japan – 日本語
- Korea – 한국어
- Latin America – Español (Latinoamérica)
- Middle East & Africa – English
- Netherlands – Nederlands
- Nordics – English
- North America – English
- Poland – polski
- Russia – Русский
- Singapore, Malaysia, and Philippines – English
- Spain – Español
- Taiwan – 繁體中文
- Thailand – ไทย
- Turkey – Türkçe
- United Kingdom – English
- Vietnam – Tiếng Việt
- EOL Products
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- RUCKUS Forums
- RUCKUS Technologies
- Access Points
- H320 Not Assigning DHCP/NAT to client machine
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
H320 Not Assigning DHCP/NAT to client machine
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-24-2019 10:37 AM
We have just added an H320 to a room to allow a user to access the wired network on site. LAN 1/LAN 2 will not assign him an address. He gets a 169 self-assigned address. I have attempted to mirror another site with this function working on an H510 and that also would not assign an IP. WiFi connectivity works fine and will assign proper IPs. I have tried with VLAN set to 1 for default and also with other various VLAN IDs on site. I cannot seem to figure out how to get this device to assign an IP. Any thoughts or advice would be appreciated.
Our Virtual SmartZone is on v5.1.0.0.4% if that is relevant.
Our Virtual SmartZone is on v5.1.0.0.4% if that is relevant.
3 REPLIES 3
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-24-2019 11:00 AM
Hi Jordan,
For AP Ethernet ports you wish to allow connect wired client devices you need to configure the port as Access with the VLAN you expect to have the client connected to on your network.
The AP will tag all traffic inbound on this wired port and the traffic will be bridged out the AP tagged as configured. The port the AP is connected through must be trunking (accept tagged traffic) for the specific VLAN.
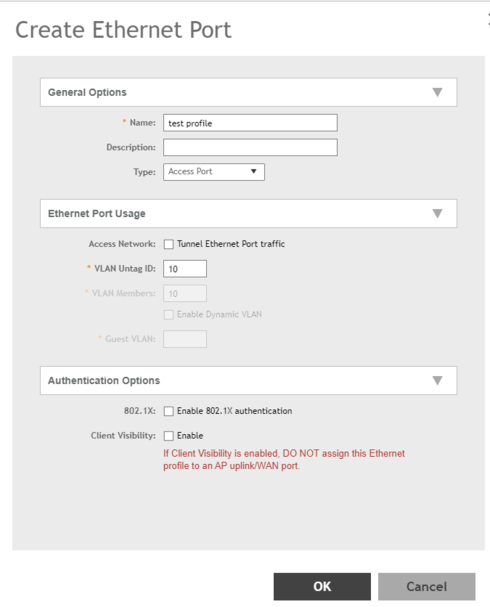
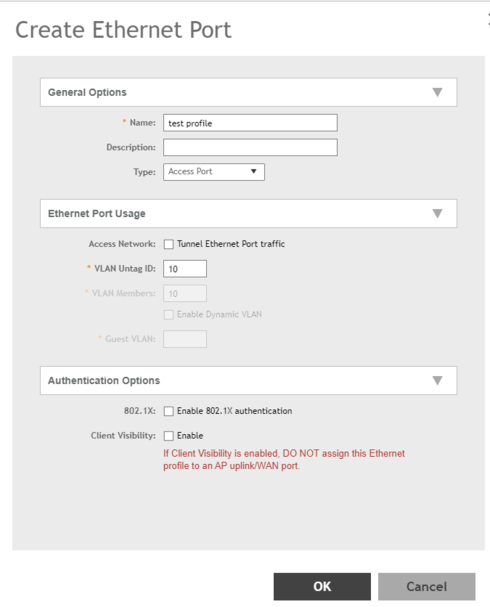
You need to first create an Ethernet Port profile, under Services and Profiles, Tunnels & Ports, Ethernet Ports. These are created per Zone
Note- if you leave VLAN1 this will put the traffic into the native/untagged VLAN on the AP WAN Ethernet port.
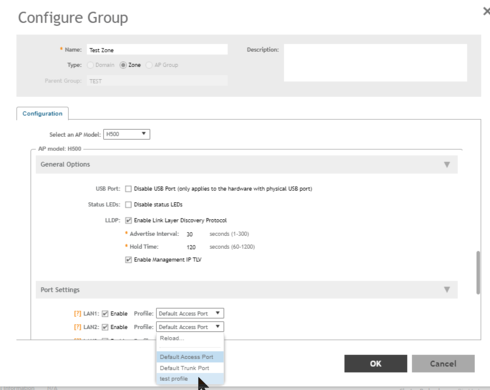
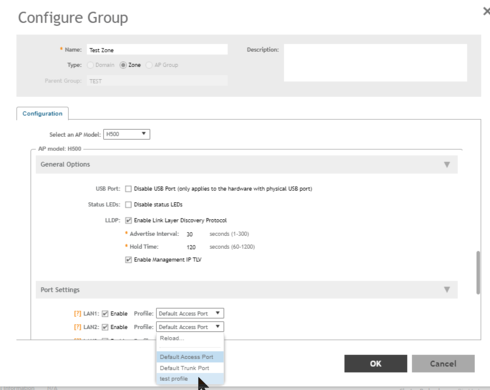
You then assign the profile to the Model Specific options for the AP Zone you are using:
If you use the same VLAN's assigned to WLAN/SSID's and they work then the wired client traffic should also be tagged with the same VLAN's and get IP's.
If you are using a Ruckus Virtual Data Plane and tunneling traffic to a central point, then the egress port of the data plane must be connected to a Trunk port that accepts the tags configured for the WLAN/SSID and/or the Ethernet ports.
Please check the following Knowledge Base articles on out support site that may be helpful:
https://support.ruckuswireless.com/articles/000009675
I hope you find this information helpful
Thanks for choosing Ruckus Networks products - a Commscope company.
For AP Ethernet ports you wish to allow connect wired client devices you need to configure the port as Access with the VLAN you expect to have the client connected to on your network.
The AP will tag all traffic inbound on this wired port and the traffic will be bridged out the AP tagged as configured. The port the AP is connected through must be trunking (accept tagged traffic) for the specific VLAN.
You need to first create an Ethernet Port profile, under Services and Profiles, Tunnels & Ports, Ethernet Ports. These are created per Zone
Note- if you leave VLAN1 this will put the traffic into the native/untagged VLAN on the AP WAN Ethernet port.
You then assign the profile to the Model Specific options for the AP Zone you are using:
If you use the same VLAN's assigned to WLAN/SSID's and they work then the wired client traffic should also be tagged with the same VLAN's and get IP's.
If you are using a Ruckus Virtual Data Plane and tunneling traffic to a central point, then the egress port of the data plane must be connected to a Trunk port that accepts the tags configured for the WLAN/SSID and/or the Ethernet ports.
Please check the following Knowledge Base articles on out support site that may be helpful:
How to configure AP Ethernet port settings
Enabled ports can be used as Trunk port, Access port, or General port. This article provides definitions and application details.https://support.ruckuswireless.com/articles/000009675
I hope you find this information helpful
Thanks for choosing Ruckus Networks products - a Commscope company.
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-24-2019 11:18 AM
Hey Albert,
Thanks for the reply, I have gone through those steps and configured these a few times previously. I see that some of my options are different from the included screenshots and want to verify the settings with you.
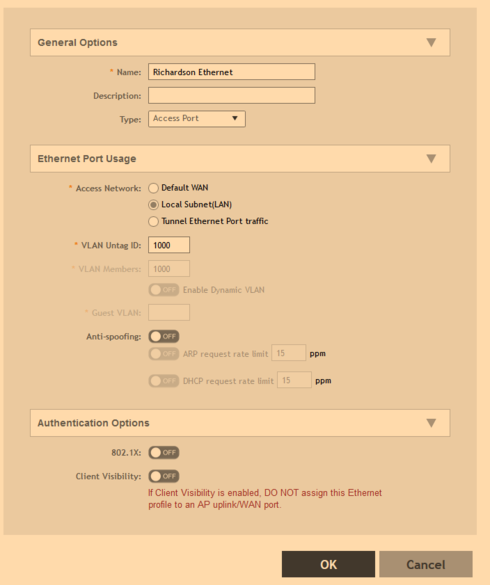
I am unsure if I should leave Default WAN selected or if I should use Local Subnet in this configuration, I feel that Local Subnet should be used to access the LAN on site and then later traverse to the WAN.
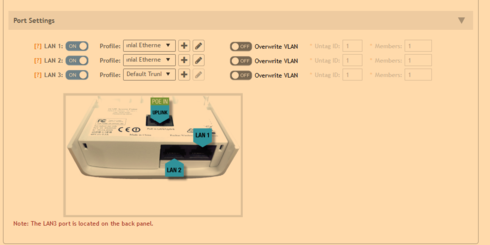
These are the settings I have previously configured and was unable to successfully connect with.
Our VLANs on site are - 10, 20, 30, 40, 50, 60, 70, 1000-1063, and 2000-2199.
Would you suggest leaving the VLAN at 1 to allow the traffic to hit the default trunk configuration which is also set to 1?
I also do not see any Data Planes configured in the interface for the site as a whole, looking under Cluster, within the System tab.
Thanks for the reply, I have gone through those steps and configured these a few times previously. I see that some of my options are different from the included screenshots and want to verify the settings with you.
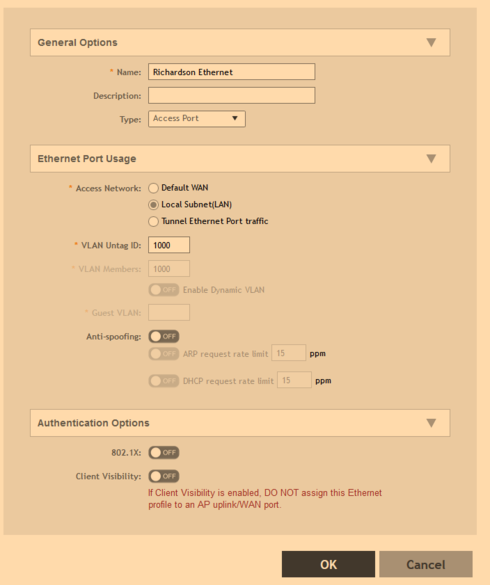
I am unsure if I should leave Default WAN selected or if I should use Local Subnet in this configuration, I feel that Local Subnet should be used to access the LAN on site and then later traverse to the WAN.
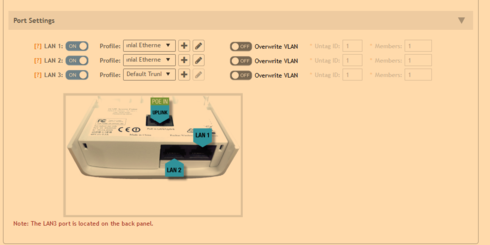
These are the settings I have previously configured and was unable to successfully connect with.
Our VLANs on site are - 10, 20, 30, 40, 50, 60, 70, 1000-1063, and 2000-2199.
Would you suggest leaving the VLAN at 1 to allow the traffic to hit the default trunk configuration which is also set to 1?
I also do not see any Data Planes configured in the interface for the site as a whole, looking under Cluster, within the System tab.
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-24-2019 11:43 AM
Hi Jordan,
The only system I had available to get screen shots is SZ 3.6.2.0.222 - so some features may have changed.
To use the Ethernet Ports as Access you should choose the "local Subnet" option. The VLAN configured in the Ethernet Services Profile will then be the VLAN that all traffic from devices on that port will be tagged when it is bridged out the AP uplink/WAN port.
The Default WAN option is for the port that connects the AP to the network and is for making that port a Trunk port that will carry all configured VLAN's (WLAN and Ethernet port). Usually this is the PoE in port.
You can configure the additional ports on an AP as Default WAN as well if you wish to connect a VLAN switch. The untagged VLAN setting will work as the Access port VLAN for untagged traffic but if other traffic is sent via this port it will be bridged with the VLANS from that switch. The switch port used for the AP uplink must be configured for these VLAN's.
Internally the AP uses VLAN 1 as the native VLAN. Configuring a WLAN or port on VLAN1 puts it into the default VLAN so it get sent out the AP untagged and will be put into the native/untagged VLAN of the Switch Port. This is most commonly used for AP management as tagging management traffic for the AP is problematic as it requires two steps when installing factory defaulted AP's (default is untagged). It really does not matter what VLAN ID you use on the switch as native on that port as the AP is not sending any tags, and the switch should then tag any incoming untagged traffic into it's native/untagged VLAN.
If you needed to use VLAN 1 as tagged (very unusual) it can be done by changing the default/untagged VLAN on the WAN port configuration.
I hope this clarifies things, but if not I will do my best to provide additional information.
Thanks.
The only system I had available to get screen shots is SZ 3.6.2.0.222 - so some features may have changed.
To use the Ethernet Ports as Access you should choose the "local Subnet" option. The VLAN configured in the Ethernet Services Profile will then be the VLAN that all traffic from devices on that port will be tagged when it is bridged out the AP uplink/WAN port.
The Default WAN option is for the port that connects the AP to the network and is for making that port a Trunk port that will carry all configured VLAN's (WLAN and Ethernet port). Usually this is the PoE in port.
You can configure the additional ports on an AP as Default WAN as well if you wish to connect a VLAN switch. The untagged VLAN setting will work as the Access port VLAN for untagged traffic but if other traffic is sent via this port it will be bridged with the VLANS from that switch. The switch port used for the AP uplink must be configured for these VLAN's.
Internally the AP uses VLAN 1 as the native VLAN. Configuring a WLAN or port on VLAN1 puts it into the default VLAN so it get sent out the AP untagged and will be put into the native/untagged VLAN of the Switch Port. This is most commonly used for AP management as tagging management traffic for the AP is problematic as it requires two steps when installing factory defaulted AP's (default is untagged). It really does not matter what VLAN ID you use on the switch as native on that port as the AP is not sending any tags, and the switch should then tag any incoming untagged traffic into it's native/untagged VLAN.
If you needed to use VLAN 1 as tagged (very unusual) it can be done by changing the default/untagged VLAN on the WAN port configuration.
I hope this clarifies things, but if not I will do my best to provide additional information.
Thanks.
Labels
-
Access points
1 -
AP Controller Connectivity
2 -
AP Management
6 -
AP migration
1 -
Authentication Server
1 -
cli
1 -
Client Management
2 -
Firmware Upgrade
2 -
Guest Pass
1 -
I live in
1 -
Installation
3 -
IP Multicast
1 -
mounting
1 -
Poe
3 -
Proposed Solution
2 -
R320 SLOW SPEED
1 -
R550
1 -
R610
1 -
R650
2 -
R750
2 -
Ruckus
1 -
Security
1 -
SmartZone
1 -
Solution Proposed
2 -
SSH
1 -
T710
1 -
Unleashed
1 -
User Management
1 -
Wireless Throughput
1 -
WLAN Management
2 -
ZoneDirector
1
- « Previous
- Next »

